At the heart of any effective cloud security strategy lies a powerful, integrated software suite known as a CWPP. The modern Cloud Workload Protection Market Platform acts as the central command and control center, providing security teams with the unified visibility and control needed to protect a diverse and dynamic fleet of cloud workloads. A CWPP is not a single tool but a multi-faceted platform designed to secure workloads throughout their entire lifecycle, from the development pipeline to runtime production. Its architecture is purpose-built for the cloud, capable of operating across multiple public clouds (like AWS, Azure, GCP), private clouds, and even on-premise virtualized environments from a single console. The overarching goal of the platform is to consolidate multiple, disparate security functions into a single, cohesive solution, reducing tool sprawl, simplifying management, and providing a holistic view of an organization’s cloud security posture. This consolidation is critical for enabling security teams to keep pace with the speed and scale of modern, agile cloud development and operations.
A comprehensive CWPP is built on a foundation of several core capabilities. The first is broad and deep workload discovery and visibility. The platform must be able to automatically discover all workloads—including virtual machines, containers, and serverless functions—across all of an organization's cloud accounts and environments, creating a real-time, comprehensive inventory. Without knowing what you have, you cannot protect it. The second core capability is proactive security posture management. This involves continuously scanning workloads and their configurations against industry best practices (like the CIS Benchmarks) and regulatory compliance frameworks (like PCI DSS or HIPAA). This helps identify and remediate security risks like overly permissive network access, unencrypted data storage, or weak passwords before they can be exploited. This capability also includes vulnerability management, where the platform scans the operating systems and application libraries within a workload for known vulnerabilities (CVEs), prioritizing them based on severity and providing guidance on remediation.
The most critical function of a CWPP is real-time threat detection and response at runtime. This is the active, defensive shield around the workload. The platform continuously monitors the workload's behavior, looking for indicators of compromise. This can include detecting malicious processes, unauthorized file modifications (file integrity monitoring), suspicious network connections, and anomalous user activity. Advanced platforms use machine learning and behavioral analytics to build a baseline of normal activity for each workload and can then automatically detect and block deviations from this baseline, providing protection against zero-day threats for which a signature does not yet exist. When a threat is detected, the platform provides detailed forensic information to help with investigation and can trigger automated responses, such as isolating the compromised workload from the network to prevent the threat from spreading, a crucial capability for containing breaches in a fast-moving cloud environment.
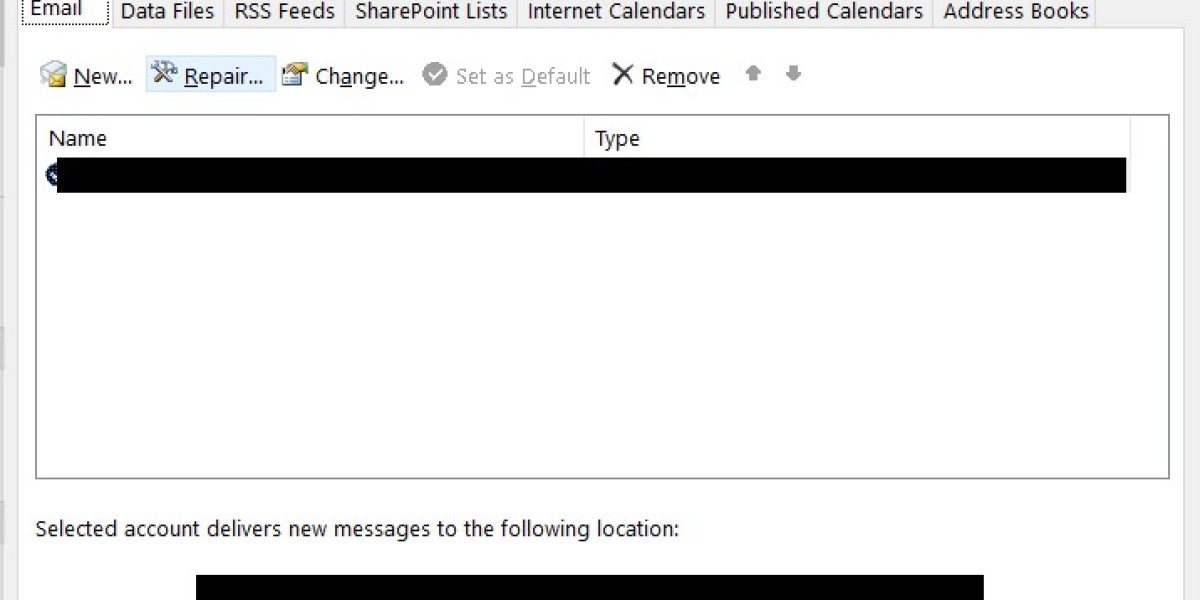
To deliver these capabilities, CWPPs typically employ one of two primary architectural approaches: agent-based or agentless. The agent-based approach involves deploying a lightweight software agent on each individual workload (e.g., on each virtual machine or container host). This agent provides the deepest level of visibility and control, as it has direct access to the workload's operating system, processes, and network stack, enabling very granular, real-time protection. The main challenge with this approach is the operational overhead of deploying and managing agents across thousands of workloads. The agentless approach, on the other hand, leverages the cloud providers' native APIs to collect data and assess the security posture of workloads without installing any software on them. This method offers much easier deployment and broader initial visibility but typically provides less real-time runtime protection compared to an agent. Many modern platforms are now offering a hybrid approach, combining agentless scanning for broad visibility and posture management with optional agents for deep, real-time protection of the most critical workloads.
Explore More Like This in Our Regional Reports: